Table of Contents
This chapter describes how to install and configure the security system in JEUS. For information about configuring other services in a domain other than what is mentioned here, refer to References.
This section will briefly summarize some basic aspects related to security system configurations.
The JEUS security system starts when the server is executed by the Security Installer. To protect JEUS, the Security Installer creates a security domain based on the information in the domain.xml file before starting the security service. The user accounts and security policies defined in the account.xml and policies.xml files are applied in the default security system.
The following two items can be configured in a security domain.
-
Definitions of security domain and security services.
-
Accounts and policies for the domain.
The following are steps for configuring the default security system.
-
Configure security domains.
-
Configure security Services for each security Domain.
-
Configure Subjects (authentication data) for each Domain.
-
Configure Policies (authorization data) for each Domain.
-
Configure additional items.
-
Configure a JavaSE SecurityManager (optional).
-
Configure a JACC provider (optional).
Directory Structure for the Default Security System
The following figure is the directory structure of the default security system. Each directory lists the configuration files used by the default security system.
JEUS_HOME/domains/<domain name>
|--config
|--security
|--security.key
|--policy
|--SYSTEM_DOMAIN
|--accounts.xml
|--policies.xml
The following describes each directory.
- security
-
Note
To apply different security policies to applications, a separate security domain directory must be created and configured.
Domains can be configured using WebAdmin or by manually modifying the domain.xml file. Other configurations, besides user account and security policy configurations, cannot be changed dynamically. Therefore, when a security domain is added or security service configurations are changed, the server must be restarted to apply the changes.
Note
All configurations related to security apply to all servers in the JEUS domain. All servers must be restarted in order to apply the security configurations, except for user account and security policy configurations.
Domain Admin Server (DAS) must be running to configure the security domain configurations, and all servers including DAS must be restarted to apply these configurations. This section describes how to define the security domain using WebAdmin or by modifying the XML file.
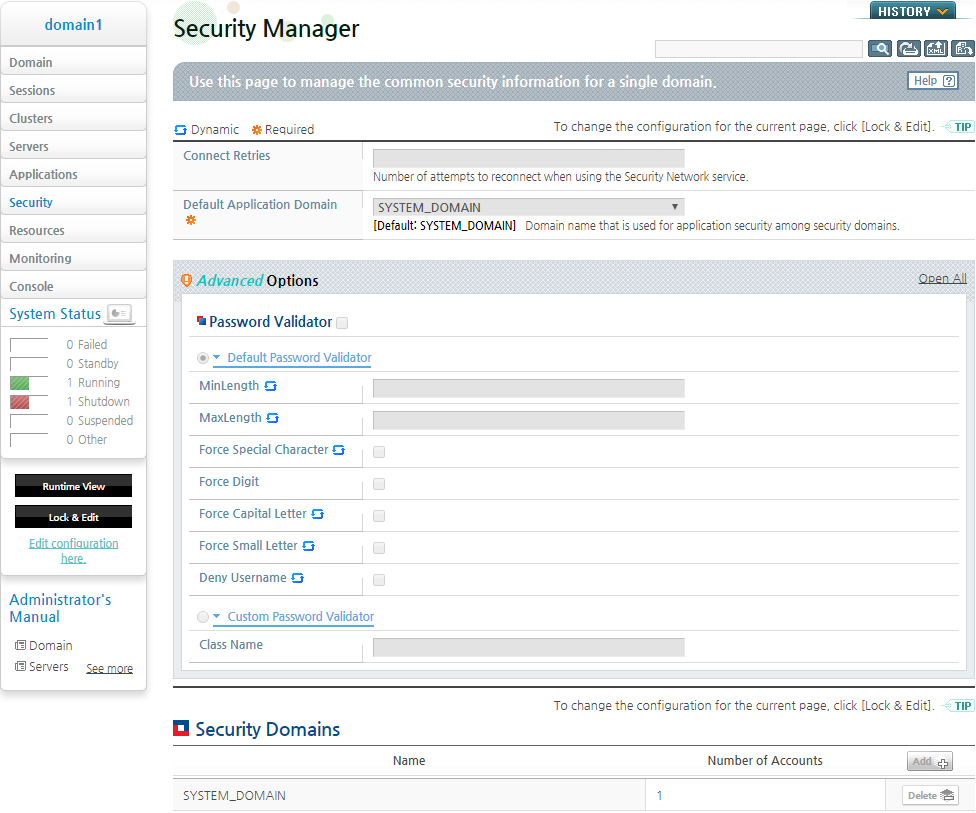
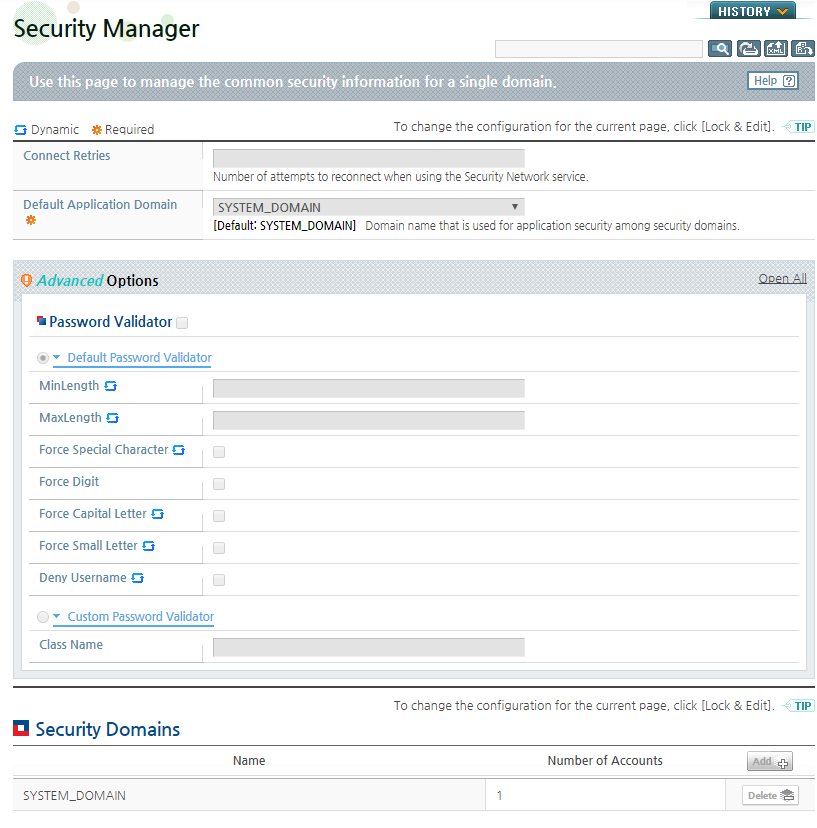
If [Security] is selected from the left menu, the security domain information will be displayed. From the list of the security domains, a domain can be specified as the 'Default Application Domain' that will be used by the applications. Domains also can be added or deleted from this screen.
The 'Connect Retries' setting is used to specify the connection retry count of JEUS Security NetworkService.
To directly modify the XML file, use the following tags from JEUS_HOME/domains/<domain name>/config/domain.xml file.
XML configuration methods for a domain are defined in jeus-domain.xsd and jeus-security.xsd in the JEUS_HOME/lib/schemas/jeus directory. The parent tag is <security-manager>, and it has the following child tags for domain configurations. Zero or more child tags can be used.
[Example 2.1] <<JEUS_HOME/domains/<domain name>/config/domain.xml>>
<security-manager>
<security-domains>
<default-application-domain>SYSTEM_DOMAIN</default-application-domain>
<security-domain> <name>SYSTEM_DOMAIN</name> ...
</security-domain> <security-domains>
</security-manager>
The following are descriptions of the configuration tags.
| Tag | Description |
|---|---|
| <connect-retries> | Sets the connection retry count in JEUS Security NetworkService (Default value: 10) |
| <default-application-domain> | Sets the default domain name that will be used in J2EE applications. (Default value: SYSTEM_DOMAIN) |
| <security-domains> | Sets the security domains that will be registered with JEUS. For more examples of <security-domains> refer to "2.3. Configuring Security Domain Components". |
This section describes how to configure user accounts and security policies using the default XML file.
It is possible to store the user account and security policy information in the database as well as in the XML file. For more information, refer to "2.5.3. Using Database" and "2.6.3. Using Database".
The following are steps to configure accounts and policies.
-
To configure a new security domain, a new directory must be created under the JEUS_HOME/domains/<domain name>/config/security directory. The name of the new directory should match the name of the domain that you wish to create. By convention, domain names use all capital letters and are appended with the string "_DOMAIN". For example, the name "DEFAULT_APPLICATION_DOMAIN" can be used as a domain name.
To create a domain with the name DEFAULT_APPLICATION_DOMAIN, execute the following command.
$ mkdir ${JEUS_HOME}/domains/domain1/config/security/DEFAULT_APPLICATION_DOMAINNote
domain1 should be replaced with the actual JEUS domain name.
-
After creating the new domain directory, you must create a number of configuration files in the directory.
The best way is to copy existing configuration files from the existing domain directory and modify these files according to your need. Enter the following commands in a single line. The following sections will explain how to modify these copied configuration files.
$ cp ${JEUS_HOME}/domains/domain1/config/security/SYSTEM_DOMAIN/*.* ${JEUS_HOME}/domains/domain1/config/security/DEFAULT_APPLICATION_DOMAINBy default, SYSTEM_DOMAIN already exists under the JEUS_HOME/domains/<domain name>/security directory. SYSTEM_DOMAIN is the domain used by the JEUS server to perform authentication and authorization. Among other things, this domain contains the JEUS system "administrator" account and permissions for starting and terminating the JEUS server.
-
The newly created domain will be applied when JEUS is restarted.
The security domain, SYSTEM_DOMAIN, will always be included regardless of the configurations in the domain.xml file. In general, you can create a directory with the same name as the domain under the JEUS_HOME/domains/<domain name>/config/security directory. In this directory, you can define the security policy information (policies.xsd) and account information (accounts.xsd) of the Repository, which needs to be defined for each domain. You can also use the domain.xml file to register the Security Service for each domain.
Note
If a security domain was added using WebAdmin in the default security system without following the aforementioned steps, the account information and security policy information in SYSTEM_DOMAIN will be shared. In order to separate the account and security policy information by security domains, you must follow the aforementioned steps.
This section describes how to configure security domain components, excluding security services.
If [Security] is selected from the left menu of WebAdmin, Security Manager page will appear. Select a security domain that needs to be changed. Configure the security domain as described in "2.2. Configuring the Security System Domain" after clicking [Lock & Edit] to change to the edit mode.
Under the Security Domains list, if a domain name is clicked, the security configuration page will appear. The security configuration page consists of the following tabs. For more information about each tab, refer to the descriptions in the following table.
| Tab | Description |
|---|---|
| [Cache Config] | Defines the cache policy value that will be applied to the security service in the domain. |
| [Key Store] | Defines the keystore file information that will be applied to the security services in the domain. |
| [Security Service] | The security services configuration page. |
| [Custom Service] | Regardless of the service properties provided by JEUS Security Framework, additional security services can be registered through the properties of the service that implements JEUS Security API. For more information, refer to "2.4. Configuring Security Services". |
| [Accounts & Policies Management] | Configures the user accounts and security policies. For more information, refer to "2.5. Configuring the Security System User Information" and "2.6. Configuring Security System Policies". |
[Cache Config]
On the Cache Config page, you can define the cache policy values that will be applied to the security services in the domain. The cache value applies to the repository service, which is one of the security services.
[Key Store]
On the Keystore Config page, you can define the keystore file information that will be applied to the security services in the domain.
The certificate information is included in the Keystore file, and the information can be used for user authentication. If child configuration values do not exist and '–Djeus.ssl.*' or '–Djavax.net.ssl.*' is not configured, the default value will be applied.
The following describes each configuration item.
| Item | Description |
|---|---|
| Keystore Path | The path to the keystore file that will be applied to the current domain. (JEUS_HOME/domains/<domain name>/config/security/keystore) |
| Keystore Alias | An alias for the keystore. When there are multiple keyEntry certificates in the keystore file, the keystore entries are accessed by their unique aliases. |
| Keystore Password | The password for the keystore file for the current domain (Default value: changeit). |
| Keystore Keypassword | The password for the keystore file for the current domain. (Default value: Same as the <keystore-password> value) |
| Truststore Path | The path to the truststore file the current domain. (JEUS_HOME/domains/<domain name>/config/security/truststore) |
| Truststore Password | Password for the truststore file for the current domain (Default value: changeit). |
[Custom Service]
On the Custom Services page, additional security services can be registered in the properties of the service that implements JEUS Security API, regardless of the service properties provided by the JEUS Security Framework. For more information about the service types provided by JEUS and Custom security service development, refer to "Chapter 5. Developing Customized Security Services".
The security services that are loaded to each security domain are defined in domain.xml as follows.
The security configurations are defined by an XML schema in jeus-security.xsd, which is under the JEUS_HOME/lib/schemas/jeus directory.
Inside the <security-domains> tag, add <security-domain> child tags related to security settings. One or more <security-domain> tags can be used, and each tag defines a security domain used in JEUS.
The following is an example of the security configuration file.
[Example 2.2] Security System Service Configurations - <<domain.xml>>
<?xml version="1.0" encoding="UTF-8"?>
<domain xmlns="http://www.tmaxsoft.com/xml/ns/jeus">
. . .
<security-manager>
<default-application-domain>DEFAULT_APPLICATION_DOMAIN</default-application-domain>
<security-domains>
<security-domain>
<name>SYSTEM_DOMAIN</name>
.....
</security-domain>
<security-domain>
<name>DEFAULT_APPLICATION_DOMAIN</name>
</security-domain>
</security-domains>
</security-manager>
. . .
</domain>
Note
Inside the <security-domain> tag, if you only configure the <name> tag and do not configure other Service Provider information, the default security services will be used for the corresponding domain.
Descriptions of child tags of <security-domain> are as follows.
-
The security domain name.
-
<cache-config> (0 or more, optional)
Defines the cache policy value that is to be applied to the security repository service in the domain.
Tag Description <min> The minimum cache entry size that will be applied to the repository service. <max> The maximum cache entry size that will be applied to the repository service. <timeout> The cache entry timeout value that will be applied to the repository service. -
<keystore-config> (0 or more, optional)
Defines the keystore file information that will be applied to the security service in the domain.
If child configuration values do not exist and '–Djeus.ssl.*' or '–Djavax.net.ssl.*' is not configured, the default value will be applied..
Tag Description <keystore-path> The path to the keystore file to be applied to the current domain.
(JEUS_HOME/domains/<domain name>/config/security/keystore)
<keystore-alias> The keystore alias. When there are multiple keyEntry certificates in the keystore file, the keystore entries are accessed via unique aliases. <keystore-password> The keystore file password for the current domain. (Default value: changeit). <keystore-keypassword> The keystore file Keypassword for the current domain
(Default value: Same with the value of <keystore-password> )
<truststore-path> The path to the truststore file for the current domain
(JEUS_HOME/domains/<domain name>/config/security/truststore)
<truststore-password>T The truststore file password for the current domain (Default value: changeit).
JEUS security system supports plugin type of authentication and authorization services. This section describes how to configure security domain components, including security services, by using WebAdmin and by modifying the XML file.
If you select the [Security Service] tab, the security service configuration page appears. The security services can be defined for each domain. The authentication and authorization processes operate differently depending on the security services of the relevant security domain.
| Menu | Description |
|---|---|
| [Authentication] | Modifies the security services related to user authentication. |
| [Authorization] | Modifies the security services related to user authorization. |
| [Identity Assertion] | Specifies the service that retrieves user name from the certificate. |
| [Credential Mapping] | Specifies the Path to the Truststore file and password for X509Certificate. |
| [Credential Verification] | Specifies the service that verifies user credential. |
| [Audit] | Specifies the service that collects information about events that occurred in JEUS Security Framework. |
| [Subject Validation] | Performs user(subject) validation. |
[Authentication]
In Security Service, if you select the [Authentication] tab, you can modify security services related to user authentication.
-
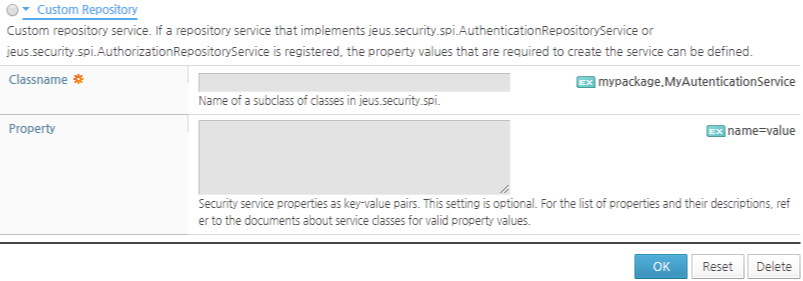
[Repository Service]
Specifies the authentication repository.
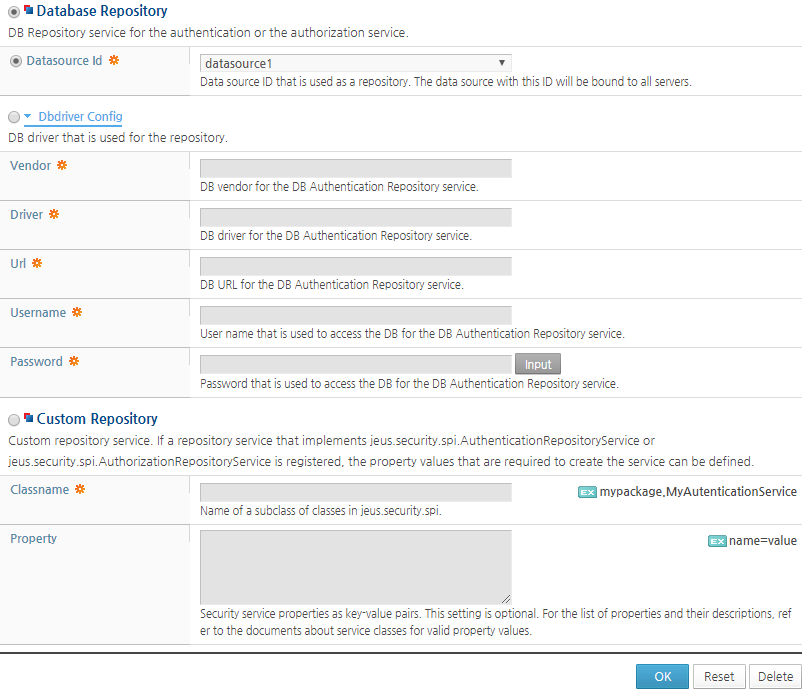
Item Description Xml File Repository Set to Xml File Repository that uses XML, by default. Specify the file name and path in the Config File section. Database Repository If checked, a database can be used as the authentication repository. Enter a 'Datasource id' defined in resources. Dbdriver Config Specifies the database driver. For more information about database table organization, refer to "2.5.3. Using Database". Custom Repository Specifies the Custom service that implements the jeus.security.spi.AuthenticationRepositoryService class.
-
[JAAS Login Config]
Sets configurations that are related to JAAS. In the 'Callback Handler Classname' field, you can define the factory class name of the Callback handler. Click [Add] to add a LoginModule. For more information about JAAS, refer to "Chapter 7. Using JAAS".
-
[Custom Authentication Service]
Defines the class name of the security service that performs user authentication. Sets the class name that implements the jeus.security.spi.AuthenticationService class. JEUS provides "DefaultAuthenticationService" as the default class name. Properties can be configured according to the implementation class.
[Authorization]
In Security Service, if you select the [Authorization] tab, you can modify security services that are related to user authorization.
-
[Basic]
As for authentication repository, one option can be selected from Xml File Repository, Database Repository, and Custom Repository.
Item Description Jacc Service Determines whether to use JACC service.
If JACC is used, jeus.security.impl.azn.JACCAuthorizationService and jeus.security.impl.aznrep.JACCAuthorizationRepositoryService, which are JEUS implementation classes, are set as authorization and repository services, respectively.
For more information about JACC, refer to "Chapter 6. Using JACC Provider".
Repository Service Sets the authorization repository. Database Repository For more information about the database table organization, refer to "2.6.3. Using Database". Custom Repository Only the custom service that implements jeus.security.spi.AuthorizationRepositoryService can be used.
-
[Custom Authorization Service]
Defines the class name of the security service that performs user authorization. Sets the name of the class that implements the jeus.security.spi.AuthorizationService class. JEUS provides "DefaultAuthenticationService" as the default class name. Properties can be configured according to the implementation class.
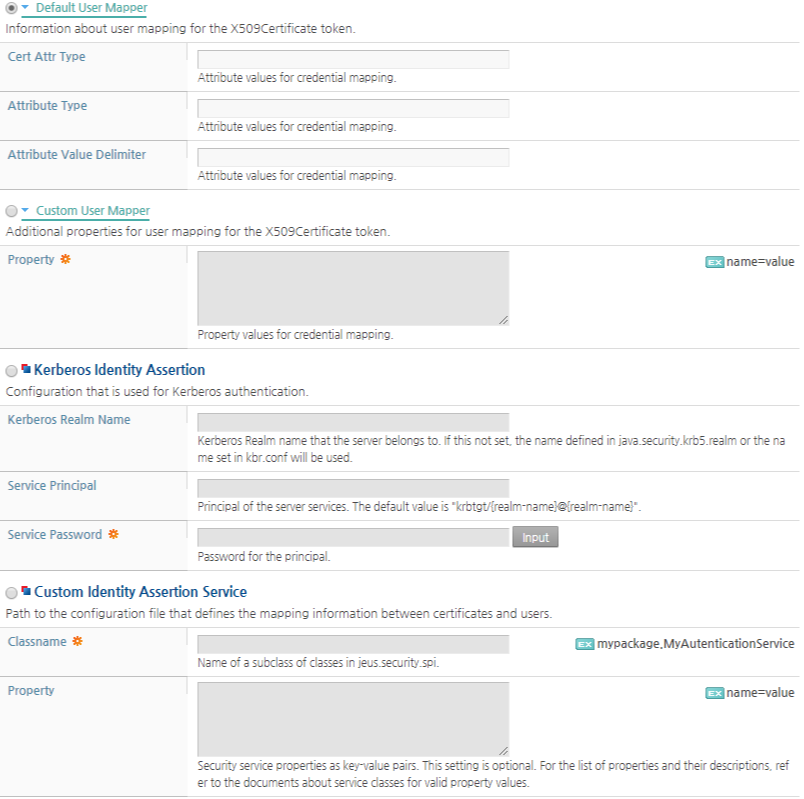
[Identity Assertion]
On the Identity Assertion page, you can specify the service that retrieves the user name from a certificate. Select one of the classes that implements jeus.security.spi.IdentityAssertionService.
 |
| Item | Description |
|---|---|
| Default Identity Assertion Service | The configuration can be modified for DefaultIdentityAssertionService, a default service provided by JEUS. This service operates based on the X509Certificate. The 'Filename' and 'Filepath' fields specifies the XML file that contains the mapping information between a certificate and user name. |
| Custom Identity Assertion Service | Defines the Custom Identity Assertion service. Specifies a class that directly implements SPI. |
| Kerberos Identity Assertion | Specifies Assertion that uses the Keberos protocol. If this configuration is set, jeus.security.impl.login.KerberosSharedStateLoginModule, among the LoginModule implementation classes that are provided by JEUS, is activated. |
[Credential Mapping]
On the Credential Mapping page, you can configure the Truststore path and password for X509Certificate.
By default, the jeus.security.impl.credmap.JKSCertificateCredentialMappingService, the default implementation class of jeus.security.spi.CredentialMappingService, is activated.
[Credential Verification]
On the Credential Verification page, you can select the service that checks the user credentials.
By default, the check box for 'Password Verification' is selected, which enables the verification of a user password. If you select the check box for 'Jeus Certificate Verification', the X509Certificate verification is enabled.
Under the Credential Verification list, you can add a class that implements the jeus.security.spi.CredentialVerificationService class by clicking [Add].
[Audit]
On the Audit page, the service that collects information about the events that occurred in the JEUS Security Framework can be set.
The file name that will store the logs and its path can be specified in the 'Filename' and 'Filepath' fields. The log level can be specified in the 'Audit Level' field. The default implementation class jeus.security.impl.auditlog.BasicAuditLogFileService is used.
Under the Custom Audit Service list, you can add the class that implements the jeus.security.spi.EventHandlingService class by clicking [Add].
[Subject Validation]
On the Subject Validation page, you can specify the validation checks for users (Subjects). If you select 'Default Subject Validation Service', jeus.security.impl.expiration.SubjectExpirationValidationService is activated, and a user validation check is performed based on whether the ExpiryTime is set or not.
Under the Custom Subject Validation Service list, you can add the class that implements the jeus.security.spi.SubjectValidationService class by clicking [Add].
The security services that will be loaded for each security domain are set in the domain.xml file as follows.
The following is an example of a security configuration file.
[Example 2.3] Security System Service Configurations: <<domain.xml>>
<?xml
version="1.0" encoding="UTF-8"?> <domain
xmlns="http://www.tmaxsoft.com/xml/ns/jeus"> . . .
<security-manager> <default-application-domain>
DEFAULT_APPLICATION_DOMAIN </default-application-domain>
<security-domains> <security-domain>
<name>SYSTEM_DOMAIN</name> <authentication>
<repository-service> <xml-file-repository>
<config-file> <filename>accounts.xml</filename>
<filepath> ${JEUS_HOME}/domains/domain1/config/security/
</filepath> </config-file> </xml-file-repository>
</repository-service> </authentication>
</security-domain> <security-domain>
<name>DEFAULT_APPLICATION_DOMAIN</name>
</security-domain> </security-domains>
</security-manager> . . . </domain>
The following are the detailed descriptions of the child tags of <security-domain> tag.
-
Name of the security domain
-
<authentication> (0 or more, optional)
Defines the cache policy value that will be applied to the security services in the domain.
-
<repository-service>
Defines the services according to the user information storage type for authentication.
Tag Description <xml-file-repository> When the user information is saved in XML file. <database-repository> When the user information is saved in database. <custom-repository> When the user information loading method is applied by implementing the extended repository service that inherits the jeus.security.spi.AuthenticationRepositoryService SPI. -
<jaas-login-config>
Registers the JAAS service that applies to the domain.
-
<callback-handler-class>: JAAS Callback Handler Factory class name.
-
<login-module>: Configuration related to the LoginModule.
Tag Description <login-module-classname> Class name that contains the package that implements the LoginModule. <control-flag> Property definition for controlling the authentication stack by defining one of the following four properties:
-
required
-
requisite
-
sufficient
-
optional
<option>(0 or more) Definitions of property values that will be applied when initializing the LoginModule. -
-
-
<custom-authentication-service>
Defined when applying the default authentication service that is extended by inheriting the jeus.security.spi.AuthenticationService SPI. Follow the Custom Security Service configuration methods.
-
-
<authorization> (0 or more, optional)
Defines the authorization service that applies to the domain.
-
<repository-service>
Defines service according to the policy information repository type used for authorization.
Tag Description <xml-file-repository> When the policy information is saved in XML file. <database-repository> When the policy information is saved in a database. <custom-repository> When the user information loading method is applied by implementing the extended repository service that inherits the jeus.security.spi.AuthorizationRepositoryService SPI
-
<custom-authorization-service>
Defined when applying the default authentication service that is extended by inheriting the jeus.security.spi.AuthorizationService SPI. Follow the Custom Security Service configuration methods.
-
<jacc-service>
Defined when applying the JACC1.5-based authorization service.
-
-
<identity-assertion> (0 or more, optional)
Defines the IdentityAssertion service that applies to the domain.
-
<default-identity-assertion-service>
Defines the basic Identity Assertion Service that is provided by the JEUS Security Framework.
-
<x509-identity-assertion>: Supports Identity Assertion Service for the X509Certificate token.
Tag Description <config-file> Specifies the location of the file that defines the information needed to perform user mapping of the X509Certificate token.
(Default value: user-cert-map.xml under the DOMAIN directory)
<default-user-mapper> Defines a delimiter for the attribute value (attribute-value-delimiter), attribute Type(attribute-type), or attribute type(cert-attr-type) value for the X509Certificate Token value.
-
-
<custom-identity-assertion-service>
Defined by implementing the Identity Assertion Service that inherits jeus.security.spi.IdentityAssertionService SPI. Follow the Custom Security Service configuration methods.
-
-
<credential-mapping> (0 or more, optional)
Defines the CredentialMapping service that applies to the domain.
-
<default-credential-mapping-service>
Supports the basic Credential Mapping Service that is provided by the JEUS Security Framework.
-
<x509-credential-mapping>: Supports the Credential Mapping Service for the x509Certificate.
Tag Description <truststore-path> Defines the path for truststore file that is to be applied to the current domain. <truststore-password> Defines the password for truststore file that is to be applied to the current domain.
-
-
<custom-credential-mapping-service>
Defined by implementing the Credential Mapping Service that inherits jeus.security.spi.CredentialMappingService SPI. Follow the Custom Security Service configuration methods.
-
-
<credential-verification> (0 or more, optional)
Defines the Credential Verification service that applies to the domain.
-
<default-credential-verification-service>
Supports the basic Credential Verification Service that is provided by the JEUS Security Framework.
Tag Description <password-verification> Defines the verification service for the PasswordFactory class. <jeus-certificate-verification> Defines the verification service for the X509Certificate. -
<custom-credential-verification-service>
Defined by implementing the Credential Verification Service that inherits jeus.security.spi.CredentialVerificationService SPI. Follow the Custom Security Service configuration methods.
-
-
Defines the EventHandlingService that is to be applied to the corresponding domain. This is used to collect information about events that occurred in JEUS Security Framework.
Tag Description <default-audit-service> Defines the event log level and the file path where event information is saved.
-
config-file: Log file path.
-
audit-level: Log level.
<custom-audit-service> Defined by implementing the Audit Service that inherits jeus.security.spi.EventHandlingServiceService SPI. Follow Custom Security Service configuration methods. -
Custom Security Services
The following describes how to configure custom security services.
-
<classname> (Required)
Name of the Java class that implements the Custom Security Service. This class should contain a default public no-argument constructor, and should inherit the jeus.security.spi package's SPI or directly inherit the jeus.security.base.Service class.
-
The jeus.security.base.PropertyHolder interface (that is implemented by the jeus.security.base.Service class) can be used to configure property as a name-value pair for security services. This property is used to initialize each of the security services.
It contains the following two child tags.
Tag Description <name> Property name. <value> (optional) String property value for the property name.
For more information about the security service types that are provided by JEUS, and custom security service development refer to "Chapter 5. Developing Customized Security Services".
In the default security configurations, user data is read from the accounts.xml file.
The following is the file path.
JEUS_HOME/domains/<domain name>/config/security/<security domain name>/accounts.xml
Here, <domain name> is the name of the domain and <security domain name> is the name of the security domain for which the users are managed.
The following describes how to configure user information using WebAdmin.
-
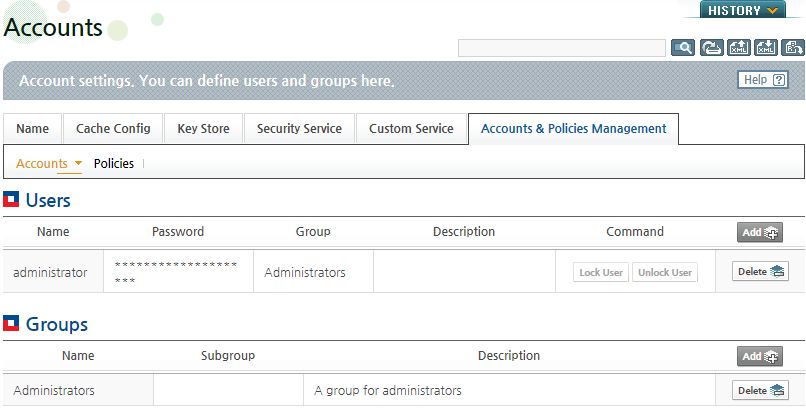
On the [Accounts & Policies Management] > [Accounts] page, you can configure the user information. It is modified dynamically. You can add or delete users by using the [Add] and [Delete] buttons.
In the Groups section, you can add and delete groups. In the Users list, a user can be added to an existing group. Groups can be added or deleted by clicking the [Add] and [Delete] buttons.
-
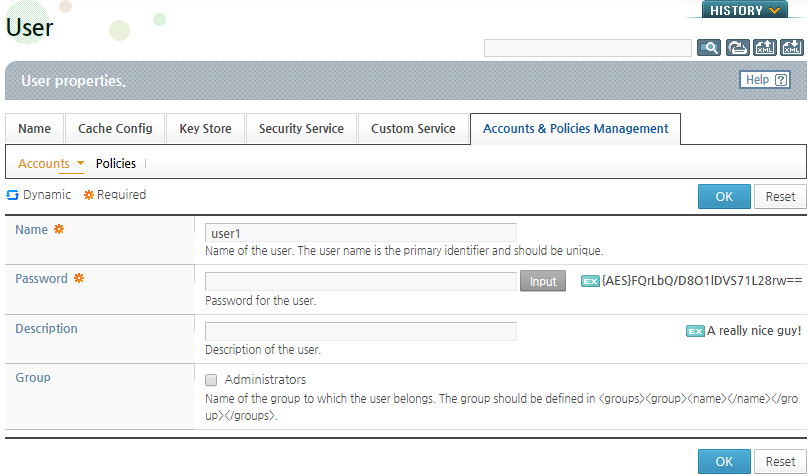
In the User list, if you click [Add], the User page appears. On this page, you can only modify the accounts.xml file, which is the default security system provided by JEUS.
-
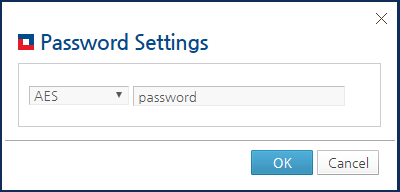
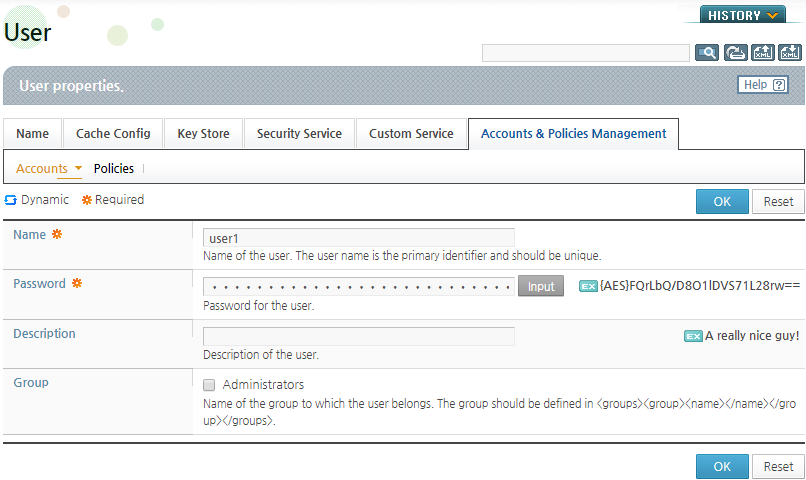
If you click [Input] to the right of 'Password', you can set the user password. Select an encryption algorithm to encrypt the password. Enter the password and then click [OK].
When the password configuration is complete, the user password will be encrypted by the specified algorithm, and the result can be checked on the following page. For more information, refer to "2.5.4. Configuring Password Security".
-
Specify the group where the user will belong to in 'Group' and click [OK].
The XML schema of accounts.xml is accounts.xsd, which is in the JEUS_HOME/lib/schemas/jeus directory.
In the accounts.xml file, there are 0 or more <user> and <group> tags inside the <accounts> tag. They represents a user and a group, respectively.
[Example 2.4] Security System User Information Configuration: <<accounts.xml>>
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<accounts xmlns="http://www.tmaxsoft.com/xml/ns/jeus">
<users>
<user>
<name>user1</name>
<password>{AES}mnG6ItxFO/WQlE2YzIZ7sA==</password>
<group>group1</group>
</user>
<user>
<name>user2</name>
<password>{DES}7dJ0KDTGQNpSnQAPYBNnmA==</password>
</user>
<user>
<name>user3</name>
<password>{DES}7dJ0KDTGQNpSnQAPYBNnmA==</password>
<group>nested_group</group>
</user>
<user>
<name>user4</name>
<password>{SEED}dl2EePMAcnxPYbIyknuZkA==</password>
<group>nested_group</group>
</user>
</users>
<groups>
<group>
<description>Group1</description>
<name>group1</name>
<subgroup>nested_group</subgroup>
</group>
<group>
<description>For NestedGroup</description>
<name>nested_group</name>
</group>
</groups>
</accounts>
The following describes configuration tags in detail.
-
Each user tag contains the following child tags.
Tag Description <description> (optional) Description of the <user> (string). <name> (required) Name of the <user>. (ex : user name, user id) <password> (0 or more, optional) Password of the <user>.
The value that is encoded by using a particular algorithm. The algorithm or encoding method applied to <password> will be specified in ’{}’. Refer to "2.5.4. Configuring Password Security".
<group> (0 or more, optional) The name of the group that the <user> belongs to. A user can be included in multiple groups. Also, the group must designate one of the groups defined in the <group> tag, described next.
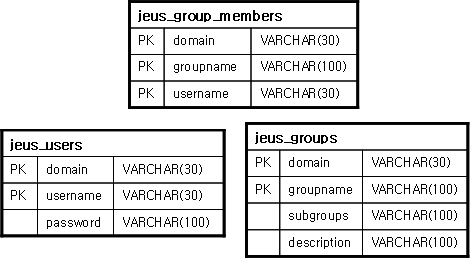
This section explains how to configure authentication using the database table defined by JEUS.
The following example illustrates how to use the data source defined in JEUS.
[Example 2.5] Configuring Users Using Database: <<domain.xml>>
<?xml
version="1.0" encoding="UTF-8"?> <domain
xmlns="http://www.tmaxsoft.com/xml/ns/jeus"> . . .
<security-manager> <seuciry-domains>
<security-domain> <name>MY_DOMAIN</name>
<authentication> <repository-service>
<database-repository> <datasource-id>auth</datasource-id>
</database-repository> </repository-service>
</authentication> . . . </security-domain>
</security-domains> </security-manager> . . .
</domain>
In the previous example, the data source ID must be configured using the <datasource-id> element. The data source ID is registered in the domain.xml file that will be used for authentication. Authentication can also be performed by directly communicating with the database through the DriverManager without using the JDBC that is provided by JEUS. To do this, change the <datasource-id> element block of the previous example as follows.
The following example illustrates how to configure the database repository when not using the JEUS JDBC.
[Example 2.6] Without Using JEUS JDBC: <<domain.xml>>
<security-manager> ... <repository-service> <dbdriver-config>
<vendor>oracle</vendor>
<driver>oracle.jdbc.OracleDriver</driver>
<url>jdbc:oracle:thin:@127.0.0.1:1521:ORA9I</url>
<username>scott</username>
<password>{base64}dGlnZXI=</password>
</dbdriver-config> </repository-service> ...
</security-manager>
Note
As applications frequently establish database connections and close them in this way, there may be some drop in performance. So, it is recommended to use JEUS JDBC (<datasource-id>) to enhance performance.
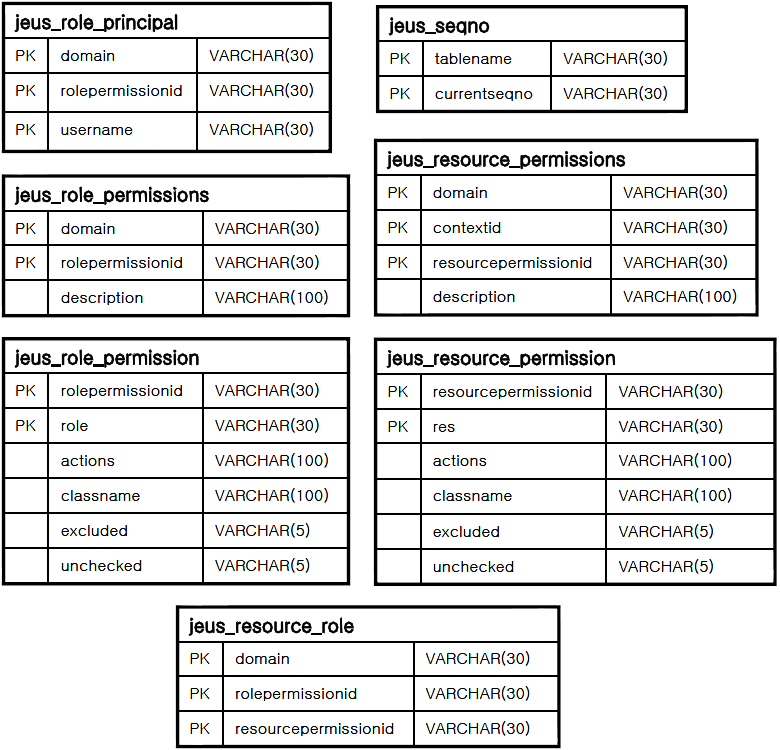
The tables that are used in the database are organized as follows:
If the tables do not exist in the database, create a DB table
by using the JEUS_HOME/templates/security/dbrealm.sql.template file.
This will initially create the user with the name 'jeus' and the
password 'jeus'.
This section describes how to check password validity, encryption algorithms, and how to manage the SecretKey file for the password security configurations.
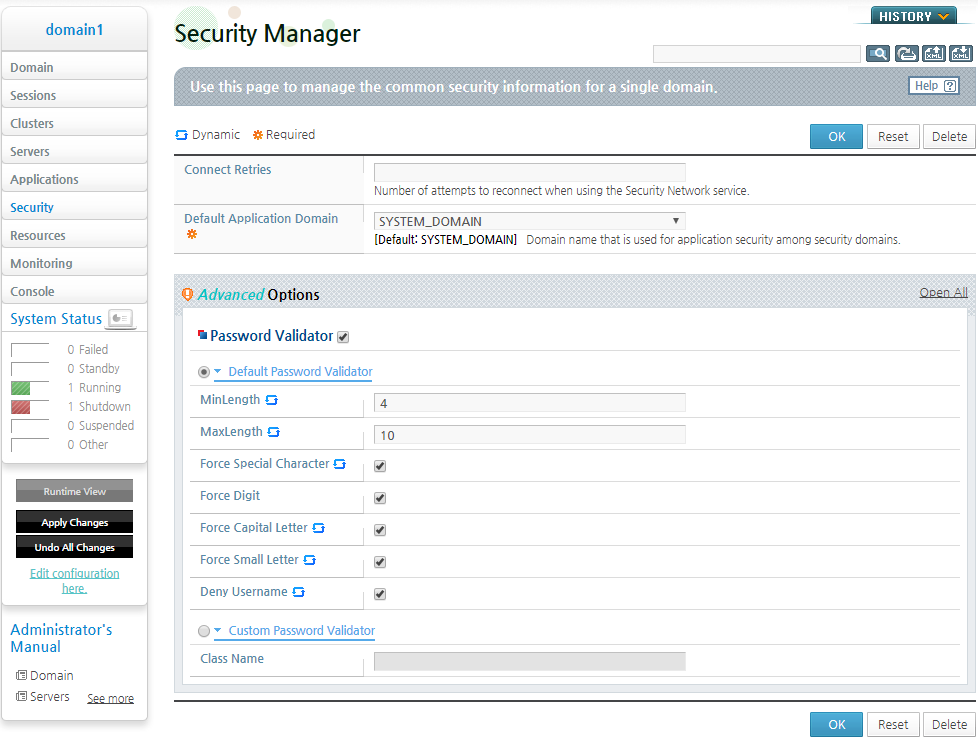
Password Validity Check
When a user enters a password to create a new account or make changes to an existing password, the validity of the password can be checked using various restrictions (such as options to use uppercase/lowercase characters, digits, and special characters and a rule that a password name must not be identical to its ID name). This improves the security of the password.
A domain administrator can select and use either DefaultPasswordValidator provided by default or CustomPasswordValidator, which is user implemented, by adding configurations for each one to domain.xml.
-
Configuring Default Password Validator
To configure Default Password Validator, select [Security] from the WebAdmin menu to view the Password Valuator page.
Click [Lock & Edit] to change to configuration mode, and then select the check box next to the Password Validator header to display the Default Password Validator and Custom Password Validator settings. Configure Default Password Validator as desired, and then click [Apply Changes] to save the configuration.
The following describes each configuration item:
Item Description MinLength Minimum length of a password. MaxLength Maximum length of a password. Force Special Character Indicates that at least one special character must be included. Force Digit Indicates that at least one numeric value must be included. Force Capital Letter Indicates that at least one uppercase letter must be included. Force Small Letter Indicates that at least one lowercase letter must be included. Deny Username Indicates that the user ID should not be included. These items can be configured with jeusadmin commands relevant to Default Password Validator, which are modify-default-password-validator, and show-default-password-validator. The information about the commands are available in JEUS Reference Book. Part II, "Console Commands and Tools".
Once the items are configured, the configurations are saved in domain.xml as in the following:
[Example 2.7] Configurations for Default Password Validator: <<domain.xml>>
<domain> . . . <security-manager> . . . <password-validator> <default-password-validator> <minLength>4</minLength> <maxLength>10</maxLength> <force-special-character>true</force-special-character> <force-digit>true</force-digit> <force-capital-letter>true</force-capital-letter> <force-small-letter>true</force-small-letter> <deny-username>true</deny-username> </default-password-validator> </password-validator> . . . </security-manager> . . . </domain>After all the configurations are saved, they are dynamically applied as password rules. These rules must be met when a user creates a new password or updates an existing one.
-
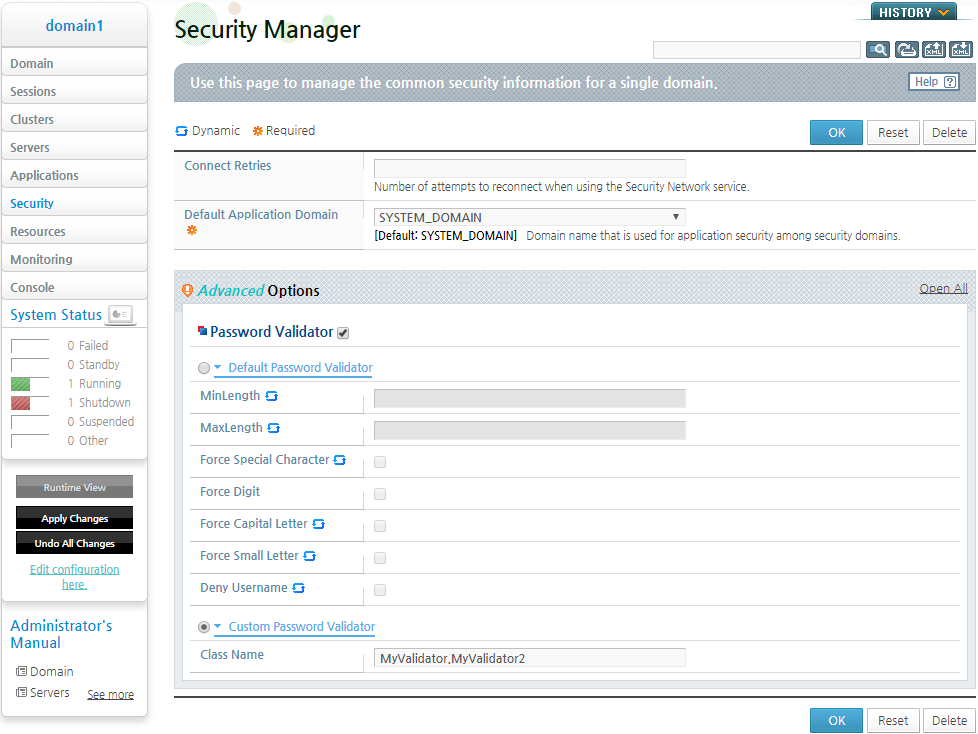
Configuring Custom Password Validator
A user can create a Custom Password Validator by implementing the jeus.util.PasswordValidator interface. Implement classes that use the interface for generating password rules, get the resulting JAR file, and place the file in the DOMAIN_HOME/lib/application directory.
The jeus.util.PasswordValidator interface is as follows:
public interface PasswordValidator { boolean validatePassword(String id, String password); }For a class that implements the PasswordValidator interface, the validatePassword(String id, String password) method takes as parameters the ID and password of the user who creates an account or changes the password. The method then checks the validity of the password and returns either true or false depending on the validation result.
Once the JAR file containing the class is placed in the DOMAIN_HOME/lib/application directory, use either WebAdmin or jeusadmin commands to configure a Custom Password Validator.
To configure it on WebAdmin, select [Security] to go to the Password Validator page.
Click [LOCK & EDIT] to change to configuration mode, and then click the checkbox next to the Password Validator header to display the Default Password Validator and Custom Password Validator settings. Select Custom Password Validator to display the Class Name field where a user can specify the class that has been implemented. More than one class can be entered by separating class names with a comma. After entering all the classes, click [Apply Changes] to save the configuration.
The following describes a configuration item:
Item Description Class Name Name of a class that implements the jeus.util.PasswordValidator interface and has been compressed into a JAR file and placed in the DOMAIN_HOME/lib/application directory. This item can be configured using jeusadmin commands relevant to Custom Password Validator, which are add-custom-password-validator, remove-custom-password-validator, and show-custom-password-validator. The information about the commands are available in JEUS Reference Book. Part II, "Console Commands and Tools".
Once the item is configured, the configuration is saved in domain.xml as in the following:
[Example 2.8] Configurations for Default Password Validator: <<domain.xml>>
<domain> . . . <security-manager> . . . <password-validator> <custom-password-validator> <class-name>MyValidator</class-name> <class-name>MyValidator2</class-name> </custom-password-validator> </password-validator> . . . </security-manager> . . . </domain>
The server must be restarted for the Custom Password Validator configuration to take effect. After the server restart, the password rules must be met when a user creates a new password or updates an existing one. If more than one class has been defined to Custom Password Validator, all password rules contained in all the classes must be met for password validation.
Note
The server will not restart if there is no JAR file of the user-defined class in the DOMAIN_HOME/lib/application directory. In this case, the user must set the relevant items in domain.xml correctly for the server to restart.
Encryption Algorithms
When configuring a user, the user password must be set. The password can be stored in plain-text, but for security reasons, it is better to encrypt the password using an encryption algorithm.
Note
It is recommended to use AES, a symmetric-key algorithm with proven reliability.
Password can be encrypted by users using the WebAdmin or the set-password command in jeusadmin. It can be encrypted directly by using the tool, JEUS_HOME/bin/encryption.
To manually encrypt the password, use the following format.
{Algorithm}Encrypted string
The key value of the symmetric-key algorithm is stored in JEUS_HOME/domains/<domain name>/config/security/security.key.
The following are descriptions of algorithms that can be used for password encryption.
The user can specify the key size for an encryption algorithm. The key size is managed as a global system property by an administrator.
The default key size is 256 bits and can be changed using the jeus.security.keylength system property. For example, the "-Djeus.security.keylength=256" option allows an encryption algorithm with a 256-bit key.
If the key size set with the system property is larger than the maximum size supported by an encryption algorithm, the supported maximum size will be used. For example, since AES supports only 128-bit, 192-bit, and 256-bit keys, AES512 will become AES256.
If a specified key size is smaller than the maximum size supported by an encryption algorithm, but is not a valid size, EncryptionException occurs. For example, since AES supports only 128-bit, 192-bit, and 256-bit keys, the AES200 setting causes EncryptionException.
Note
After the jeus.security.keylength system property is modified, passwords must be initialized.
SecretKey File Management Using The Master Password
When encrypting a password using the encryption tool (located in JEUS_HOME/bin), the SecretKey information that is applied to an encryption file can be stored in security.key file grouped by algorithm types. A master password can be used to encrypt the security.key file.
The security.key file is placed in the following path. When configuring a domain environment, the security.key file must be moved to another node.
JEUS_HOME/domains/<domain name>/config/security/security.key
When you encrypt the DB password, which needs to be registered in JEUS, a client needs a key to decrypt it. At this point, you can configure the secret key file path by using the system property.
When the master password is specified in the secret key file, this master password can also be configured using the system property. The property name for the key path is jeus.security.keypath. To specify the master password, use the jeus.security.master property. These properties can also be used when starting JEUS. However, for security reasons, it is recommended to use the prompt (standard input) to enter the master password.
The user information must be entered when starting a server using the JEUS script or by accessing the server using jeusadmin. In such case, the user information can be cached so that the user information does not need to be entered every time.
Note
The information is stored encrypted in Base64 in USER_HOME/.jeusadmin/.jeuspasswd. Since the Base64 encoding is not secure and is used to store sensitive user information, ID/password, it is not recommended for use.
Only the login information, that was authenticated, is stored in the cache.
When executing the connect command in jeusadmin, if the option -cachelogin is added with the user information, the login information will be stored in the file. When JEUS script is used, the login information is stored using the key, <domain name>:<server name>.
When JEUS script is executed, if login information with the same domain and server name exists, the user information will be automatically filled without having to re-enter the user information. If the user manually enters the information, even if there is already cached login information, the cached information will be ignored. Jeusadmin stores the login information using the <host>:<port> key of the sever, which you are trying to access.
The following example shows the stored login information.
[Example 2.9] Stored Login Information: <<.jeuspassword>>
#Warning: We don't recommend to use this on Production Environment. localhost:9736 amV1czpqZXVz domain1:server1 amV1czpqZXVz
The stored login information can be deleted using the remove-login-cache command, an off-line jeusadmin command.
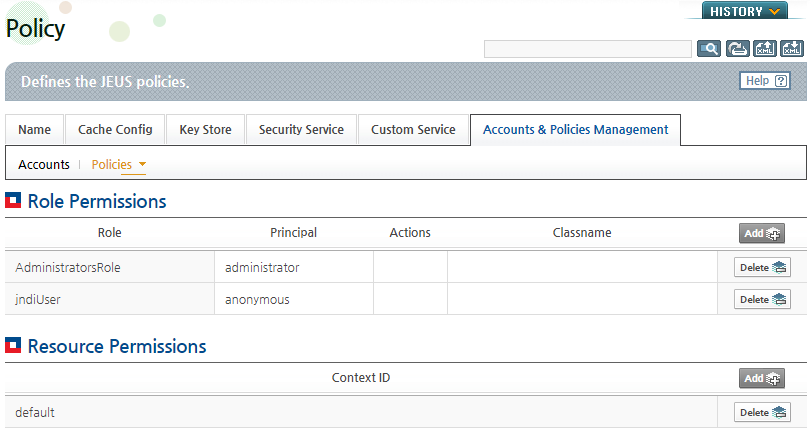
When configuring default securities, the policy data (authorization data) is read from the file, policies.xml.
The file is in the following path.
JEUS_HOME/domains/<domain name>/config/security/<security domain name>/policies.xml
<domain name> is the domain name, and <security domain name> is the domain name where the policy will be applied.
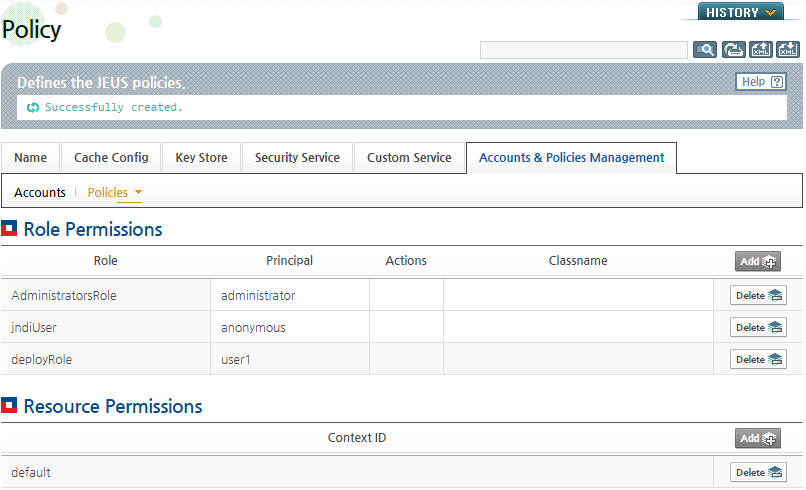
In the [Accounts & Policies Management] tab, if you select [Policies], security policies can be configured. In the Role Permissions section, principals can be mapped to roles. Multiple principals can be mapped to a role. The mapped principals inherit the role's permissions.
If you click [Add], you can add a principal-to-role mapping.
Note
Like other user information configurations, only the policies.xml file that is provided by the default JEUS security system can be changed from this page.
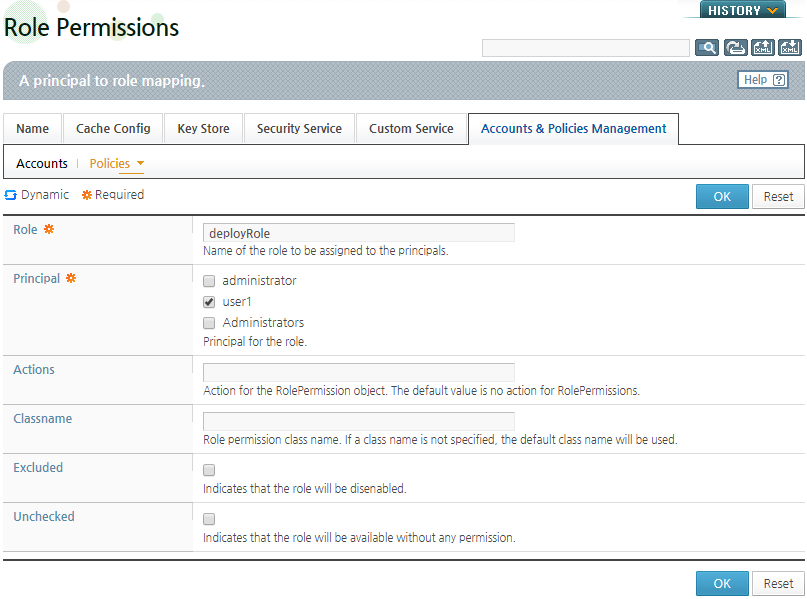
Role Permission Registration
Under the Role Permissions list, you can register a role permission by clicking [Add].
After entering a name in 'Role', select the Principal that will be granted the role permission. To deny access to the role, select the check box for 'Excluded'. To allow access to the role, select the check box for 'Unchecked'. After completing the configurations, click [OK].
Resource Permissions Registration
The following shows how to register Resource Permissions.
-
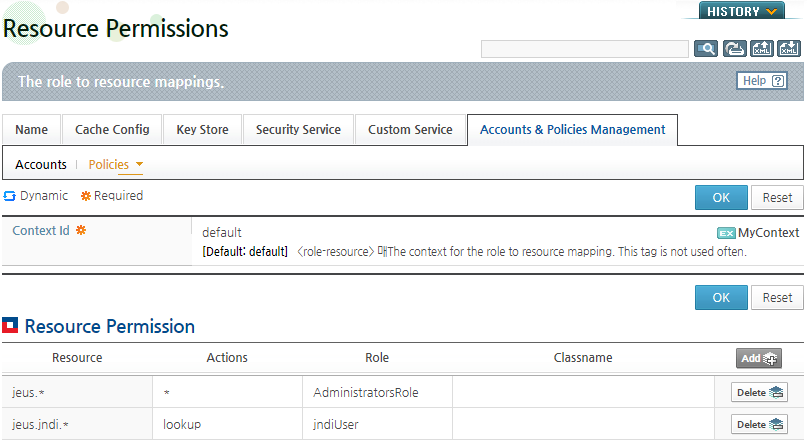
To grant resource permission to a role, select 'default' under Resource Permissions. Context ID is used to identify security policies, and 'default' is the Context ID of the security policy that is used in the default JEUS security system.
-
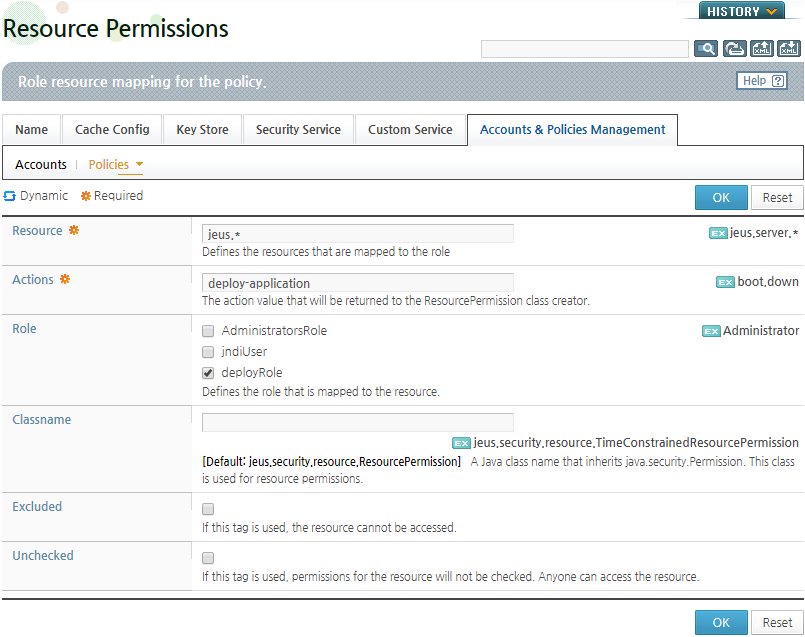
The default Context ID can be used to configure resource permissions for the JEUS system. Under the Resource Permissions, a role-to-resource mapping can be added by clicking [Add].
-
On the Resource Permissions page, enter the resource name and actions, select the roles for the resource, and then click [Add]. As in the Role Permission configurations, to deny access to the resource, select the check box for 'Excluded'. To allow access to the resource, select the check box for 'Unchecked'. For the list of JEUS resource permissions, refer to "Appendix B. JEUS Server Permissions".
The XML schema of the policies.xml file is policies.xsd, and it is in the JEUS_HOME/lib/schemas/jeus. policies.xml directory.
It consists of multiple <policy> tags and each tag represents individual policies (authorization data). Each <policy> tag consists of the following child tags.
[Example 2.10] Security System Policy Configurations: <<policies.xml>>
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<policies xmlns="http://www.tmaxsoft.com/xml/ns/jeus">
<policy>
<role-permissions>
<role-permission>
<principal>user1</principal>
<role>administrator</role>
</role-permission>
<role-permission>
<principal>user1</principal>
<role>teller</role>
<actions>9:00-17:00</actions>
<classname>
jeus.security.resource.TimeConstrainedRolePermission
</classname>
</role-permission>
</role-permissions>
<resource-permissions>
<context-id>default</context-id>
<resource-permission>
<role>teller</role>
<resource>bankdb</resource>
<actions>select, update</actions>
</resource-permission>
<resource-permission>
<role>administrator</role>
<resource>jndi</resource>
<actions>modify, delete</actions>
</resource-permission>
<resource-permission>
<resource>jndi</resource>
<actions>lookup</actions>
<unchecked/>
</resource-permission>
<resource-permission>
<role>administrator</role>
<resource>jeus.*</resource>
<actions>*</actions>
</resource-permission>
</resource-permissions>
</policy>
</policies>
The following describes configuration tags.
-
Provides information about principal-to-role mappings. Multiple <role-permission> tags are nested inside this tag.
The <role-permission> tag consists of the following child tags.
Tag Description <principal> (0 or more) Principal name that owns the current role-permission. <role> (1ea, required) Role name. <actions>(optional) Actions for the Role. <classname>(optional) The Java class name that implements java.security.Permission, which will be used for role permission. If omitted, by default, jeus.security.resource.RolePermission is used. For more information about configuring Custom Permission, refer to Custom Permission implementation and configurations. <excluded>(optional) Empty tag ( <xxx/>) with no value. If specified, the role permission is excluded (this means that the role implied by the permission will be granted to no one).<unchecked>(optional) Empty tag. If specified, the role permission is unchecked (this means that the role implied by the permission will be granted to everyone). -
<resource-permissions> (0 or more)
These tags contain information about role-to-resource mapping as follows:
-
<context-id> (optional)
Context ID (string). Context is the scope for authorization checks. The default Context ID for JEUS resources used by JEUS system is "default".
-
<resource-permission> (0 or more)
The <resource-permission> tag consists of the following tags.
Tag Description <role> (0 or more) Role name that owns the current resource-permission. <resource> (1ea, required) Resource name. <actions> (optional) Actions for the resource. <classname> (optional) The Java class name that implements java.security.Permission which will be used for Resource Permission. If omitted, by default, jeus.security.resource.ResourcePermission is used. For more information about configuring Custom Permission, refer to Custom Permission implementation and configurations. <excluded> (optional) Empty tag with no value. If specified, the resource permission is excluded. (this means that the resource implied by the permission will be granted to no one). <unchecked> (optional) Empty tag with no value. If specified, the resource permission is unchecked. (this means that the resource implied by the permission will be granted to everyone).
-
Normally the policies.xml file is exclusively used to configure permissions for JEUS Server Resource (like JNDI, JMS, Security Server, etc.), and NOT for J2EE application modules. To configure J2EE application module permissions, you should use various DD (deployment descriptor) files. For more information, refer to "Chapter 3. Configuring Security for Applications and Modules".
Custom Permission Implementation and Configurations
Whenever a permission (role permissions or resource permissions) is added to the policies.xml file, the Java class name of the permission must be specified. This is the name of a Java class that extends the java.security.Permission abstract class. Create a customized implementation subclass that extends the java.security.Permission Permission class, and specify the implementation class name in the <classname> tag of policies.xml.
This sub-section describes how to develop a new customized role permission that meets the following requirements. The new role permission should imply another role permission only if the following two conditions are met.
-
The other role has the same role name as this permission.
-
The current time is between the specified time limits (example: 9 am and 5 pm).
The following shows an example of a banking application where a role permission grants the principal user2 the teller role only during the 9 to 5 business hours.
To accomplish this, you must complete the following 2 steps.
-
Create the Custom Permission. Then, compile the class with javac and set the class path within the JEUS server class path.
Configure the Permission in the policies.xml file. The following implements the Custom Permission class that meets the aforementioned requirements. Code details have been omitted.
[Example 2.11] Custom Permission Class: <<TimeConstrainedRolePermission.java>>
package jeus.security.resource; import java.security.Permission; import java.util.Calendar; import java.util.StringTokenizer; /** * A time-constrained Role permission. * <p> * With this permission implementation you can express * things such as "X can only be in the role Y between * 09:00 AM to 05:00 PM". */ public class TimeConstrainedRolePermission extends RolePermission { private String timeConstraint = "*"; private int startTime = Integer.MIN_VALUE; private int endTime = Integer.MAX_VALUE; public TimeConstrainedRolePermission(String roleName) { this(roleName, "*"); } public TimeConstrainedRolePermission(String roleName, String timeConstraint) { super(roleName); if (timeConstraint != null) { this.timeConstraint = timeConstraint; parseTimeConstraint(); } } private void parseTimeConstraint() { . . . } public boolean equals(Object anotherObject) { . . . } public int hashCode() { . . . } public String getActions() { return timeConstraint; } public boolean implies(Permission anotherPermission) { if (this.timeConstraint.equals("*")) { return super.implies(anotherPermission); } else { Calendar cal = Calendar.getInstance(); int curHour = cal.get(Calendar.HOUR_OF_DAY); int curMinute = cal.get(Calendar.MINUTE); int now = curHour * 60 + curMinute; if (now >= this.startTime && now <= this.endTime) { return super.implies(anotherPermission); } else { return false; } } } }
The previous class inherits the jeus.security.resource.RolePermission class, which in turn inherits the java.security.Permission class. This structure promotes code reusability.It is also possible to create another java.security.Permission class by inheriting the TimeConstrainedRolePermission class.
In the previous example, there are two types of constructors.
-
The first has one parameter (role name).
-
The second has two parameters (role name, time constraint)
In java.security.Permission class, the first parameter is name, and the second parameter is actions. Some permission implementation classes omit the second constructor that receives the actions parameter.
-
The actions parameter contains the valid time period for the permission, and it has the value “09:00-17:00”.
-
The name parameter represents the role name, such as administrator or teller.
-
The heart of the implementation is in the "implies(Permission anotherPermission)" method, which first checks whether the current system time is within the given time constraints. And, if so, it delegates the call to the super class by calling the super.implies() method, and if not, it returns "false". All implies(..) method should return a boolean value, and whether the relevant Permission implies the Permission object passed to it.
Note
1. For more information about the implies() method and the abstract class java.security.Permission, refer to Java SE Javadoc documents.
2. For more information about jeus.security.resource.RolePermission, jeus.security.resource.TimeConstrainedRolePermission, and jeus.security.resource.ResourcePermission classes, refer to Reference and jeus.security.resource package in JEUS Security Javadoc.
-
-
Configure the policies.xml file to use permissions.
[Example 2.12] Custom Permission Class: <<policies.xml>>
<?xml version="1.0" encoding="UTF-8" standalone="yes"?> <policies xmlns="http://www.tmaxsoft.com/xml/ns/jeus"> <policy> <role-permissions> <role-permission> <principal>user2</principal> <role>administrator</role> <actions>9:00-17:00</actions> <classname> jeus.security.resource.TimeConstrainedRolePermission </classname> </role-permission> </role-permissions> <resource-permissions> <context-id>default</context-id> <resource-permission> <role>administrator</role> <resource>jeus.*</resource> <actions>*</actions> </resource-permission> </resource-permissions> </policy> . . . </policies>The user, user2, is in the administrator role during the business hours of 9 am to 5 pm. The administrator role has the right to perform any actions (‘*’) on all JEUS resources (‘jeus.*’). Therefore, user2 can perform any operations on all JEUS resources during the business hours.
The previous rule also applies when configuring JEUS DD file in J2EE application and module. Naturally, the rule also applies to role-to-resource permission and to principal-to-role permission as shown in the previous example. For more information about using customized permissions in JEUS DD, refer to "Chapter 3. Configuring Security for Applications and Modules".
In order to configure the policy using a database, domain service must be configured in the domain.xml file as in the following. In order to directly use the driver manager, add the <dbdriver-config> tag, instead of the <datasource-id> tag, as for the authentication setting. However, it is recommended to use JEUS JDBC data source for performance benefits.
[Example 2.13] Configuring Policies Using Database: <<domain.xml>>
<?xml version="1.0" encoding="UTF-8"?>
<domain xmlns="http://www.tmaxsoft.com/xml/ns/jeus">
...
<security-manager>
<security-domains>
<security-domain>
<name>MY_DOMAIN</name>
<authorization>
<repository-service>
<database-repository>
<datasource-id>auth</datasource-id>
</database-repository>
</repository-service>
</authorization>
. . .
</security-domain>
</security-domains>
</security-manager>
. . .
</domain>
A URL, username, and password to access the JDBC driver, which accesses the database, are required to use the AuthenticationRepositoryService that uses a database.
In the following example, a password that is encoded in Base 64 must be entered to access the Oracle DB. When entering a password applied with a certain encryption algorithm or encoding method, use the same method as for user password of accounts.xml.
The database tables have the following structure.
If the tables do not exist in the database, create a DB table
by using the JEUS_HOME/templates/security/dbrealm.sql.template file. The
basic policy is granted the administrator role in “SYSTEM_DOMAIN”,
thereby possessing Resource authority for “jeus.*”. The default
principal included in the administrator role is jeus as mentioned in
"2.5.3. Using Database".
This section describes how to add additional configurations other than subject and policy.
The use of a JavaSE SecurityManager in JEUS can increase the platform reliability, but might undermine the performance. Usually, all core JEUS codes as well as the J2EE application and module code deployed to JEUS may be treated as completely “trusted” code, and thereby avoid the overhead incurred by the SecurityManager. This mode of operation, with no SecurityManager, is the default mode in JEUS.
However, there may be cases where the increased reliability and code-level security provided by a JavaSE SecurityManager is considered more important than the performance enhancement.
For example, the administrator may have to deploy some untested or otherwise suspicious JavaEE applications or modules to JEUS. In such case, it may be desirable to protect your machines and environment by boosting the code level protection at the expense of performance by using JavaSE SecurityManager.
In order to use a JavaSE SecurityManager with JEUS, define jvm-option in the domain.xml file for a particular server as follows.
-Djava.security.manager
-Djava.security.policy=${JEUS_HOME}/domains/domain1/config/security/policy (in UNIX)
The policy file is JEUS_HOME/domains/<domain name>/config/security/policy and the its content is as follows:
[Example 2.14] Java SE SecurityManager Configurations: <<policy>>
grant codeBase
"file:${jeus.home}/lib/system/*" { permission
java.security.AllPermission; }; grant { permission
java.net.SocketPermission "127.0.0.1:1024-", "connect, accept,
connect, listen, resolve"; permission
java.security.SecurityPermission "runTrustedLogin", "read";
permission java.security.SecurityPermission "loginCodeSubject",
"read"; permission java.security.SecurityPermission
"putProviderProperty.*"; permission java.security.SecurityPermission
"insertProvider.*"; permission javax.management.MBeanPermission "*",
"*"; };
The JavaSE SecurityManager is completely independent from JEUS security system. The JEUS security system does not provide protection at the code level (permission configuration that can execute code), but instead it provides security at the user level (the identity of the process that is running and what it is allowed to do).
The only overlap between the two is that, under special conditions, the JEUS security system can check with the JavaSE SecurityManager for some code level permission (see above) in order to protect JEUS from malicious or bug-filled Servlet and EJB code.
For details of configuring the JACC 1.5, refer to "Chapter 6. Using JACC Provider".
If IdentityAssertionService is supported, it is read from the cert-user-map.xml file that contains the mapping information between a certificate and user. The file is in the following location.
JEUS_HOME/domains/<domain name>/config/security/<security domain name>/
The <domain name> tag is for the domain name and the <security domain name> tag is for the security domain where the user belongs to. The XML schema of the cert-user-map.xml file is cert-user-map.xsd, which is in the JEUS_HOME/lib/schemas/jeus directory.
In the file, the parent tag, <cert-user>, can have <user>, <cert>, and multiple <cert-user> child tags. Each contains the property information for user to certificate mapping.
[Example 2.15] Configuring Information to Grant Identity: <<cert-user-map.xml>>
<?xml
version="1.0" encoding="UTF-8" standalone="yes"?> <cert-user-map
xmlns="http://www.tmaxsoft.com/xml/ns/jeus"> <cert-user>
<username>user1</username> <cert>
<subjectDN>user1DN</subjectDN> </cert> </cert-user> </cert-user-map>
Each <cert-user> tag has the following child tags.
-
Each <cert> tag has the following child tags, which define the certificate mapping information for the user. It defines the value that maps to user name using child attribute value that ensure a unique ID for granting the identity of the certificate, which is included in the truststore file.
Tag Description <alias>(optional) Defines the alias for certificate within the keystore. (string) <subjectDN>(optional) Defines the subejctDN for certificate the within keystore. (string) <SKI>(optional) Defines the SKI for certificate within the keystore. (string) <issuer>(optional) Defines the certificate issuer within the keystore. (string) <serialNo>(optional) Defines the certificate serial number within the keystore. (string)
The JEUS security system provides an API, through the UserCertMappingService, that can be used to obtain certificate information of the authenticated user's identity. If UserCertMappingService class is supported, the user data is read from the user-cert-map.xml file, where additional mapping information exists for the certificate grouped by users. The file is in the following path.
JEUS_HOME/domains/<domain name>/config/security/<security domain name>/
The <domain name> tag is for the domain name and the <security domain name> tag is for the security domain that the user belongs to. The XML schema of user-cert-map.xml is user-cert-map.xsd, and its path is JEUS_HOME/lib/schmas/jeus.
In the file, the parent tag, <user-cert-map>, can have 0 or more <user-cert> tags. Each contains the property information to obtain a user certificate from the Keystore file.
[Example 2.16] Configuring the Certificate Information for Identity: <<user-cert-map.xml>>
<?xml
version="1.0" encoding="UTF-8" standalone="yes"?>
<user-cert-map xmlns="http://www.tmaxsoft.com/xml/ns/jeus">
<user-cert>
<username>user1</username>
<alias>alias1</alias>
<keypassword>changeit</keypassword> <secretkey>
<keyname>testkeypass</keyname>
<keyalgorithm>AES</keyalgorithm>
<keyvalue>bjhTUjJvSXRTOGlkVEdlNHJnM2N3VnljSDZXV0JkYz0=</keyvalue>
</secretkey> </user-cert>
</user-cert-map>
Each <user-cert> tag has the following child tags.
-
Defines the user name for the certificate within the keystore. Since this is the primary identity, it must be unique. (ex: user name, user ID)
-
Defines the alias for certificate within the keystore.
-
Defines the keypassword to obtain the private key of the certificate within the keystore. (ex: changeit)
-
Defines the private key.
Each <secretkey> tag has the following child tags.
Tag Description <keyname> (required) Defines the name of the private key. The keyname inside <user-cert-map> tag must be unique. (string)
<keyalgorithm> (required) Indicates the key algorithm for the private key. (string) <keyvalue> (required) Shows the private key value in the Base64 format.
![[Security Service] - [Cache Config]](resources/figure_cache_config.png)
![[Security Manager] - [Key Store]](resources/figure_key_store.png)
![[Security Manager] - [Custom Services]](resources/figure_custom_service.png)
![[Security Service] - [Authentication]](resources/figure_authentication_xml_repository.png)
![[Security Service] - [Authentication] - [JAAS Login Config]](resources/figure_jaas_login_config.png)
![[Security Service] - [Authentication] - [Custom Authentication Service]](resources/figure_custom_authentication_service.png)
![[Security Service] - [Authorization] - [Basic]](resources/figure_authorization_xml_repository.png)
![[Security Service] - [Authorization] - [Custom Authorization Service]](resources/figure_custom_authorization_service.png)
![[Security Service] - [Identity Assertion]](resources/figure_default_identity_assertion_service.png)
![[Security Service] - [Credential Mapping]](resources/figure_credential_mapping.png)
![[Security Service] - [Credential Verification]](resources/figure_credential_verification.png)
![[Security Service] - Audit](resources/figure_audit.png)
![[Security Service] - [Subject Validation]](resources/figure_subject_validation.png)